***
Bu yazı DÖDER’ in e-dergisi Denizden için yazdığım denizlerde siber güvenlik yazısının İngilizcesi çevirisi. Denizden dergisinde gelecekte bu yazı İngilizce olarak yayınlanır mı bilmiyorum, ama bu yazıyı yazma fikri ve yazmak için yaptığım araştırma kafamda bir sürü yeni araştırılacak konu oluşturdu ve bir sürü ilginç bilgi toplamamı sağladı. Bu yazı, sonrasında bu konuda yazmayı planladığım başlıkların temelini oluşturduğu ve yazının son halini de pek beğendiğim için İngilizce halini burada yayınlamaya karar verdim. Çünkü bu konunun gelecek yazıları, bu yazıyı okurken yazıda hissedilen boşlukların ve kafanızda oluşacak soru işaretlerinin üzerine inşa edileceği için bu projenin temelini herkese göstermek istedim. (this paragraph is the translation of the below paragraph)
This article is the English translation of the “cyber security at sea” article I wrote for DÖDER’s e-magazine Denizden. I don’t know if this article will ever be published in English in Denizden magazine in the future, but the idea of writing this article and the research I did to write it, created a lot of new topics in my mind and enabled me to collect a lot of interesting information. Since this article forms the basis of the subjects I plan to write on this subject later, and as I liked the final version of the article, I decided to publish the English version here. Because the future articles on this subject will be built on the gaps felt in the article and the question marks that will arise in your mind while reading this article, I wanted to show everyone the basis of this project.
***
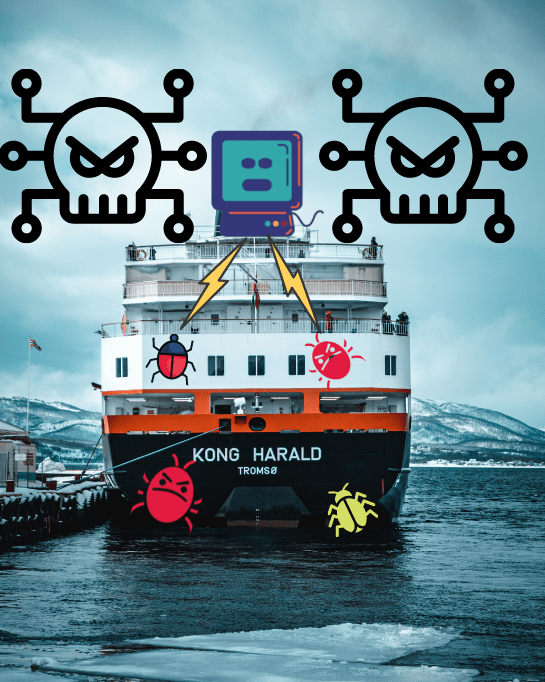
Cyber security is a subject that its importance is not known enough even today. Its importance is growing day by day in all sectors and the number of employees is increasing. We can see that many large companies do not give enough importance to this issue from the events that happened to them. But what happens when the data that needs to be protected is much more than bank accounts, personal photos, credit card information and passwords? If the data that needs to be protected is a multimillion-dollar ships data, data recorded by an ROV/AUV (Remotely Operated Vehicle/ Autonomus Underwater Vehicle), or vital data such as the amount of air in a scuba tube shown on a diver’s watch, then the subject becomes “Cyber Security at Sea”, which most people never even dream of.

With the development of technology, we have heard new concepts such as “autonomous ships”, “wireless ROVs / AUVs”, “remote control valves”, “intelligent dive computers / wacthes”, “wireless research buoys”. Each of these are great developments in their respective branches. So what do developments like these have in common, other than salt water? Each are potential targets for a hacker. Technological research companies predict that by 2025, cyber attackers will use OT (Operational Technology) environments to cause physical harm to humans. As sailors, we are included in this equation. But the question is, from a seafarer’s point of view, did we become a part of cybersecurity because of emerging technologies and wireless data transmission, or was it already a part of us?
Governments, Big Corporations, Big Ships and Big Bucks
When a cyber attacker looks at the sea, instead of metal piles floating in salt water, that person sees computers floating in salt water and the people who operate these computers. When he looks a little more carefully, he sees floating computers carrying valuable cargo. For people all over the world, maritime transport is a wheel that must turn constantly to provide access to products in distant places. Terms, deadlines and lots contracts which has many zeros. Each of these are topics that cyber attackers can target to achieve their own goals.
But Why?
As for the companies, there are big bucks and deadlines for the tasks to be complete depending on the conditions. As for the data, there is data that both states and malicious entities would like to have. These data and the way of accessing that data have both monetary and power value. Attackers can target multiple nerve points to manipulate companies the way they want. While research data is a information that needs to be unspoilt and contain high accuracy. Distortion of this type of data and non-public research data carry high monetary potential to some eyes. Technological devices that can be remotely controlled and transmit data can easily cause financial or hardware damage, with the future plan made according to the distorted data it transmits and by simply stopping working at the wrong time. As part of the maritime industry, you may be part of a reputable institution with a certain reputation, in which case you are also a representative of that institution. You are also a part of the communication and functioning of the institution you are a part of. In the background this makes you as a person, a target as the institution you represent. At the same time, each employee of the institutions is a gateway to access the data within the institution of which they are a part.
How to Hack A Ship?
Today, every person performs most of their communication via digital devices. In this way, everyone on board turns into a potential gateway for targets such as partial information of the ship, initial access to wireless networks on board, internal company data. In this regard, the tactics of the attacker can change in many ways, depending on his purpose and detailed target information. But the precaution that the end user can take in this regard is the basic individual cyber security precautions and awareness. The responsibility of the company is to arrange the wireless networks and devices on the ship with a cyber secure approach, to create cyber security awareness in its employees and to have cyber security procedures for them to follow.

So how to hack a floating computer? It’s very simple, same as a non-floating computer. We can think of ships as complex computers containing many electronic circuits, processors and sensors. We know that our computers can be hacked by clicking on a wrong link or plugging in an infected usb. The same goes for a floating computer. For yachts that can be partially controlled with a tablet, a malware that is known as “ECHOBOT”, which is a variant of “mirai”, targets web servers, video conferencing systems, modems that provide remote access to the yacht. GPS, which is frequently used on yachts and ships, has already become the target of both bug hunters and cyber attackers. When it comes to cyber security at sea, many people must first think of GPS. In 2013, a group of Texas university students managed to deflect a yacht 30 miles by hacking the GPS of a 65-foot $80M yacht and thereby deceiving the crew. Of course, this is only valid for non-physical navigation situations where bearing cannot be taken, which actually might be quite often when you are in the ocean.
Petya/ NotPetya/ EternalBlue
Lars Jensen, one of the founders of the Danish cyber security company CyberKeel, said that when they offered the system security test (pentest) to shipping companies around 2014, when they first established the company, he often heard answers such as “don’t waste your time, we are quite safe, there is no need” and that these answers are now getting lesser and lesser. This is actually pretty funny because the cybersecurity world hasn’t quite turned its eyes to the sea.
To Transfer or Not To Transfer, Is That The Question?
Can a hacker enter a ship and play with the settings of the digital instruments used on the ship, where there are various security measures, a lot of people, and the people in critical places and the time they will be found are predetermined by a schedule? Or the real question is, does he need to set foot on the ship to perform such a job? With the developing technology, ships are becoming a part of the internet where we spend our hours on. Control systems on a ship can often have an internet connection these days. If any device somehow has a wi-fi feature and can connect to the internet, that device can easily be the target of attacks over the internet. Devices such as sensors that transmit data via Bluetooth are an easy target for a security researcher who knows where to look, with a chain attack of one of the ship’s crew members hacking their personal phone in the first place.
Electronic mapping systems (ECDIS) on board ships, receive chart or software updates in several ways. They can receive updates directly via a computer connecting via USB, CD or satellite, or by connecting via the modem on the ship. Vehicles that communicate wirelessly in the ship and personal technological tools of the ship’s personnel should always use different networks. In an industry where time is money, we must be aware that cyber security does not start with the digital environments on board, but with our own personal data and personal communication tools. Ships as equipments, companies as employees, and seafarers as knowledge are very inadequate in cyber security and therefore they are very open targets for attacks.

What I have mentioned in this article does not even make up the initial letters of the whole “Cyber Security at Sea” topic. In my opinion, since the maritime industry is relatively introverted and has a separate terminology, targets that could be subjected to successful attacks “as if taking candy from a baby” were not even thought yet by the attackers. Although imaginary wall of ours has protected the maritime industry to this day, it is only a matter of time before we get a real “cyber hit” and the issue gains the importance it deserves with the popular industrial internet of things (IIOT) and developing autonomous ships. “Cyber attacks resulting in human mortality”, which is seen as a prophecy of cyber security, seems to be getting closer to our reality with the development of autonomous ships and cars. Today, we can see the emergence of the concept of “car hackers”, but there is no such concept as “ship hacker” yet. Maybe we can even expect the first ship hackers to be naval mechanical engineering students who can be considered as people of both worlds. At the Pwn20wn hack event, Tesla organized competitions in which it gave the Model 3 vehicle and $ 500,000 prize money to the person who could hack the Model 3 vehicle in order to improve the security. And there were those who hacked the car and won the prize. No one has ever heard of an event like this being held for ships anywhere in the world. It is surprising that the production of a ship and its customers are much more detailed and important than a sedan car, but that it does not receive the same attention and importance.

Apart from these, structures that can be controlled remotely such as ships or naval platforms or connected to the internet, security of devices such as ROV and marine sensors, manipulation of data transfer processes and data collection processes, hacking of a smart dive watch or dive computer and manipulation of the dive chart and old dive data in it are just a few of the issues that cyber security at sea will bring to us in the future. In 2020 “A.R.M.S.” the remote pentesting (penetration test) on ships with a software, became popular with the emergence of the corona. Which is one of the subjects that started to receive the importance it deserves from these crazy and new topics and started to make a lot of money on it. In the future, we will see, as I say “wet hackers” will have a very crazy business area. Emphasizing this concept is an opportunity for all young people, especially maritime students. When the subject starts to get the attention it deserves, the whole IT world will jump on it. If you want to take the stage of hacking the sea, there is only one rule right now, and that is to think outside the box.
Press “enter” to take the stage